You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
work passwords
- Thread starter Briansol
- Start date
- Replies 88
- Views 4K
We may earn a small commission from affiliate links and paid advertisements. Terms
Thats not unusual B....
90 days here, can't repeat the same one 3x, 1 cap 1 number 1 symbol and atleast 8 characters long.
90 days here, can't repeat the same one 3x, 1 cap 1 number 1 symbol and atleast 8 characters long.
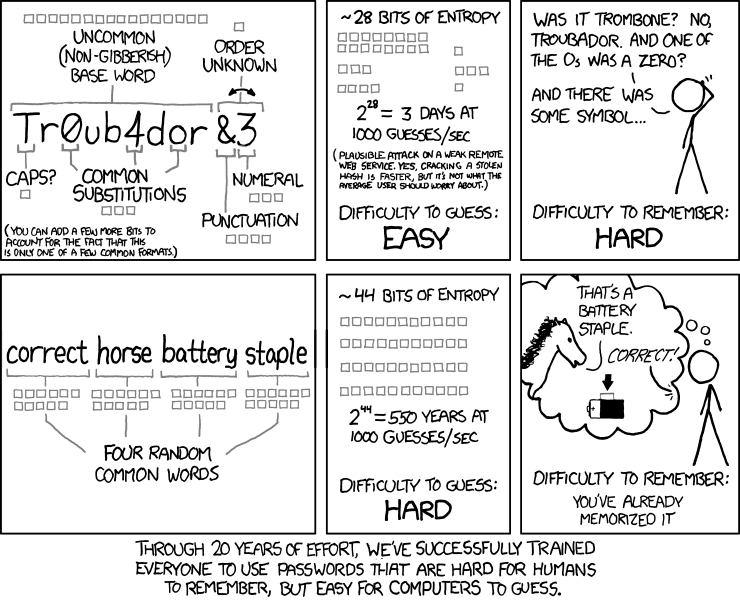
First off, this image is absolutely appropriate. I'd love to use passphrases instead of my current 'pseudo-passphrase'.
Second, password change policies are ridiculous these days. SAS70 requirements, and to some extent, PCI requirements, are actually causing more security holes than needed. Let me explain:
Let's say for example, you have 5 common passwords for different things (I'd like to think most IT people follow this rule).
1) Email
2) Work Creds
3) Bank
4) Shopping (Amazon, Verified by Visa, Newegg, etc)
5) Throw away
My throwaway creds are just that. Throw away. If someone has access to that password it nets them very little usable information.
Email. If I start finding composed emails I didnt write. I can change all my email passwords and be done with it.
Bank. Chase has password requirements that don't fall in line with any password I've ever used since the beginning of time. I made up a new password for them years and years ago. Looking back, im kinda glad they suck since it forced me to use a different password for banking.
Shopping. It lets me login to my shopping sites, which store no credit card info, without wondering 'oh god what did i pick' and if someone were to get into an account, I can just change them all. No big deal.
The last one is work. It's fucking stupid what these security compliance companies have forced us into. I've worked in IT for almost a decade now, and the policy is archaic, based on a time when people used simple words for passwords. Most people nowadays know that 'password' is not a good password. Most auth systems wont allow you to use that password anyway. The reason these policies exist though, is quite unfortunate.
Even at a large tech-centric company you still have sales people that are fucking computer retards. "Oh cindy, I've never heard of her, but she's sending me a presentation. It's in a zip file...nothing strange about that...let me just uncompress and open this .exe power point." The more frustrating part is the default windows setting that 'hides extensions for known file types'. GREAT!!!!! Now people see a file named JUST presentation and not presentation.exe, and open it not realizing it's an executable, even if they're smart enough to know the difference.
In this SPECIFIC scenario. Password changes are required. Primarily to close any back doors created by the phisher. If all passwords in a database are expired, you've effectively removed their entry point, and forced them to start their phishing over again.
What I'd really like to see SAS do is allow you to have a secondary password strength test like 'length over 30 characters >= 8 character mixed type'. The reason being is that NO ONE now gens rainbow tables without the entire UTF-8 character set. And if they do, they at least have every character on the US keyboard.
So as Randall says, these days you're probably safer using a passphrase than a complicated difficult to remember password. You're just causing more stress to yourself and making your password easier to guess.
Last edited:
can't add digits... pass can't match any of the past 12 more than 70% or something stupid like that.
there's a pin for laptop sign on (at dos prompt)
there's a pin for the vpn (luckily, this matches the laptop)
there's a keychain vasco 6 digit key to logon to said vpn that changes every 10 seconds.
the screen saver is set to come on after 3 min of inactivity (and i can't change it). Being as i don't use my laptop much use he client-supplied desktop), i literrally login and out 50 times a day, or get distracted and lose productivity so i can move my mouse on the other machine when it dims (a 10 second warning).
it won't take a lot of patterns either
weio2390%^ was a favorite back in the day, but it recognizes patterns too and won't take that and many others like it
it's rediculous.
there's a pin for laptop sign on (at dos prompt)
there's a pin for the vpn (luckily, this matches the laptop)
there's a keychain vasco 6 digit key to logon to said vpn that changes every 10 seconds.
the screen saver is set to come on after 3 min of inactivity (and i can't change it). Being as i don't use my laptop much use he client-supplied desktop), i literrally login and out 50 times a day, or get distracted and lose productivity so i can move my mouse on the other machine when it dims (a 10 second warning).
it won't take a lot of patterns either
weio2390%^ was a favorite back in the day, but it recognizes patterns too and won't take that and many others like it
it's rediculous.
can't add digits... pass can't match any of the past 12 more than 70% or something stupid like that.
there's a pin for laptop sign on (at dos prompt)
there's a pin for the vpn (luckily, this matches the laptop)
there's a keychain vasco 6 digit key to logon to said vpn that changes every 10 seconds.
the screen saver is set to come on after 3 min of inactivity (and i can't change it). Being as i don't use my laptop much use he client-supplied desktop), i literrally login and out 50 times a day, or get distracted and lose productivity so i can move my mouse on the other machine when it dims (a 10 second warning).
it won't take a lot of patterns either
weio2390%^ was a favorite back in the day, but it recognizes patterns too and won't take that and many others like it
it's rediculous.
Ah ha! They obviously want you to write down your password and stick it to your laptop!
My new work system is >=8 chars, 1 number minimum, must have >4 characters different from the last password. I've been taking the easy way out for years and just incrementing a number on the end of my work password, so now I have to change my password twice every time:
Old password
Change to new temporary password
Change to old password + 1
It does nothing other than make me waste more time at work.
Password must change every 90 days, and I've been incrementing the same password every time... I'm up to 43. That just about checks out, I've been there almost 10 years now!
Last edited:
At my job we change passwords every 90 days. It has to have 2 caps, 2 lowercase, 2 numbers, 2 special characters, at least 8 characters long and can't be the same as your last 20 passwords. I've found a solution. write down a list of 20 passwords that fit the requirements in order from 1 to 20. When it asks you to change your password change it to #1 on the list then go in and change it to #2 and so on until you get to #20 then once more to the original password that you had at the start. Keep the list and repeat the process when it makes you change your password again. It might take a few minutes to do, but at least it's like you never actually changed it so you can keep using the same password for the next 90 days.
i make patterns on the keyboard
plenty secure
easy to remember
tons of possible combinations

I do the same thing, generally some form of zigzag pattern holding shift at certain times to get caps and symbols.
Easiest passwords to remember as all I have to know is the starting key and the pattern.
15 char minimum:
2 upper
2 lower
2 numbers
2 special characters
Can't start with number
Can't match more than 6 characters of any recent (past 25) passwords
must change every 60 days for normal user, 45 for administrators (it's really 60+1 and 45+1 in practice)
Make a skip-code based on the date. Circle the date when you change your password. Add in a replacement code of several word's letters, based on the date. Make a rainbow table-ish kind of thing. Write cryptic reminders as hints.
What's the max password length?
Luckily for me, the DoD has a big push towards PKI, so all I have to remember is my PIN most of the time.
2 upper
2 lower
2 numbers
2 special characters
Can't start with number
Can't match more than 6 characters of any recent (past 25) passwords
must change every 60 days for normal user, 45 for administrators (it's really 60+1 and 45+1 in practice)
Make a skip-code based on the date. Circle the date when you change your password. Add in a replacement code of several word's letters, based on the date. Make a rainbow table-ish kind of thing. Write cryptic reminders as hints.
What's the max password length?
Luckily for me, the DoD has a big push towards PKI, so all I have to remember is my PIN most of the time.
RFID + randomized keypad + almost 20 character password that changes every 45 days, can't reuse within 6 years. Write it down, go to jail.
Similar threads
- Replies
- 0
- Views
- 3K
- Replies
- 8
- Views
- 4K